Introduction
- Tcpreplay Usage
- Tcpreplay Edit
- How To Install Tcpreplay On Windows10
- How To Install Tcpreplay On Windows 10
- With that said, you’ll need Cygwin to compile/run tcpreplay. You’ll also need to install Winpcap - the port of libpcap for Windows. For whatever reason, it seems important that you install the Winpcap files in the Cygwin root directory (/Wpdpack). Be sure to install both the driver and DLL files AND developer pack.
- Hi, On the online manual, it was mentioned that to install tcpreplay on Windows, I will 'need to install Winpcap the port of libpcap for Windows. For whatever reason, it seems important that you install the Winpcap files in the Cygwin root directory (/Wpdpack).' What is meant by installing the winpcap files in the Cygwin root directory?
Dismiss Be notified of new releases. Create your free GitHub account today to subscribe to this repository for new releases and build software alongside 50 million developers.
ZeroLogon can be used to exploit a serious vulnerability in Windows DomainControllers.
I was recently asked if you could detect a ZeroLogon attempt using aSensorFleet-based Sensor. It is easy because we have plug & play support forEmerging Threats intrusion detection ruleset andZeroLogon was added to the ruleset on September 14th 2020.
Emerging Threats can be enabled in our IDS Rule Manager-and Suricata IDS Instruments.
Here’s how you do it. We’re going to assume that basic Sensor configuration isalready done.
Step 1: Install Rule Manager and Suricata
There are few easy steps to take if you don’t haveIDS Rule Manager andSuricata IDS already enabled:
- Navigate to SensorFleet Fleet Management UI
Choose your target Sensor, and choose Add Instrument from the dropdown menu
Click Add instrument for Suricata and IDS Rule Manager

Step 2: Configure a capture interface for Suricata
Even if you don’t have it already done, setting up traffic monitoring is abreeze. It is enough to choose the capture interface since SensorFleet CaptureEngine is usually already configured as part of standard Sensor configuration.
Locate Suricata IDS from your Fleet Management UI and choose Configure fromthe dropdown menu (it might display an error status due to missing captureinterface - that’s normal).
Choose Add Interface, select Sensor bridge, type some interface name, onlychoose capability RX and hit Create.
Suricata status will change to OK after the configuration:
Step 3: Add Emerging Threats ruleset
Downloader Instrument is enabled as part of standard Sensor configuration and itgives you a centrally controlled way to fetch external configuration, such asthe Emerging Threats ruleset. You just need to add a new source and theDownloader will do the heavy lifting.
Locate IDS Rule Manager Instrument from Fleet Management UI and click the UIbutton
Click Add rulesource
Type settings for the rulesource:
With these settings, the URL will be checked for updates with HTTP HEAD every3600 seconds, and downloaded only when file changes.
After a while, you will see the Emerging Threats rules in Rule Manager UI.
Just in case, you can search the ruleset to find the ZeroLogon Rule. Open Rulesearch and type zerologon to show the zerologon rules.
Step 4: Testing the rule
It is always a good idea to test your ruleset.
Right now, the easiest way to test it against ZeroLogon detection would be toreplay a traffic capture (pcap) that should trigger the alert. Luckilythere is a pcap that does just this.
There is another way -launch a live attack against your Windows Domain Controller.I wouldn’t try that in production though.
We’re going to try the pcap. This assumes you only have a single bridge in yoursetup.
- Login to your sensor using SSH.
- List active bridges:
- Install tcpreplay utility:
- Grant permissions to write to the bridge interface from host.
- Download the test pcap to your sensor.
The exploit in pcap uses the IP addresses 172.16.0.10 and 172.16.5.58.Those should be included in your Sensor’s homenets. Add 172.16.0.0/21 toyour Sensor homenets: Choose configure from the Sensor dropdown menu, openSettings tab, add home network 172.16.0.0/21 and Save.
- Replay the pcap file to your bridge interface
Open Suricata IDS events page. You should see events like these:
Final words
Running Suricata in your network can be very useful. With good quality freerules like Emerging Threats, you can catch a lot of badness in your networkbefore things get out of control. If you see such an event, there might be stilltime to shutdown or disconnect the servers and create last minute snapshots ofthe data before the attacker installs a cryptolocker software or some othermeans to disrupt your business.
- Downloads
- Installation
Downloads
Download Releases for Users
- Latest release:
- Previous release:
- Old Win32 release
- Note that Windows is not supported by the maintainer
Download Source for Developers
Compiling source from GitHub has more requirements than compiling a release.Specifically you must have AutoGen installed. If you plan to contribute you musthave AutoGen version 5.16.2, otherwise your pull requestsmay be rejected.
If you want to help develop Tcpreplay visit our Developer Wiki.
- Download via GitHub
git clone https://github.com/appneta/tcpreplay- Or if you plan to contribute someday simply fork the repo and submit a pull request whenyou are ready to share your changes with us
- Or download the latest master tarball
- Note that master is always production ready, but not necessarily the latest stable release. See GitHub networkto see the state of master
Installation

Simple directions for Unix users
You will need to compile the source code, but first you must ensure that you havecompiling tools and prerequisite software installed. For example, on a baseUbuntu or Debian system you may need to do the following:
Next extract tarball, change to root directory, then do:
Optionally you can run the tests to ensure that your installation isfully functional:
Installation Video
Build netmap feature
This feature will detect netmapcapable network drivers on Linux and BSDsystems. If detected, the network driver is bypassed for the executionduration of tcpreplay and tcpreplay-edit, and network buffers will bewritten to directly. This will allow you to achieve full line rates oncommodity network adapters, similar to rates achieved by commercial networktraffic generators.
Note that bypassing the network driver will disrupt other applicationsconnected through the test interface. For example, you may see interruptionswhile testing on the same interface you ssh’ed into.
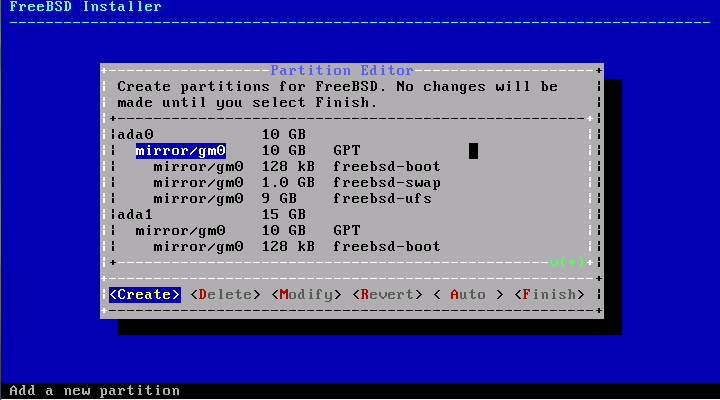
FreeBSD 10 and higher already contains netmap capabilities and will be detectedby configure. To enable netmap on the system you will need torecompile the kernel with device netmap included.
For Linux, download latest and install netmap from http://info.iet.unipi.it/~luigi/netmap/If you extracted netmap into /usr/src/ or /usr/local/src you can build without extraconfigure options. Otherwise you will must specify the netmap source directory, for example:
You can also find netmap source at http://code.google.com/p/netmap/
Netmap Installation Video
Advanced Options
There are quite a few configure time options for tcpreplay which allow you to control a lotof things. Some of the more interesting ones are:
- –enable-debug – useful for debugging bugs and crashes.
- –enable-64bits – use 64 bit counters to handle large pcap files & looping
- –enable-libnet – link to libnet. Note that libnet support has been deprecated due tovarious bugs which have not been fixed in over a year.
- –with-libnet – specify root path to libnet (something like –with-libnet=/usr/local)
- –with-libpcap – specify root path to libpcap
- –with-netmap – specify root path to netmap
- –with-tcpdump – specify path to tcpdump executable
- –enable-tcpreplay-edit – compile tcpreplay with packet editing support
Tcpreplay Usage
You can also manually select a particular method to inject packets:
- –enable-force-pf – force tcpreplay to use Linux’s PF_PACKET to send packets
- –enable-force-bpf – force tcpreplay to use Free/Net?/OpenBSD or OS X’s BPF interfaceto send packets
- –enable-force-libnet – force tcpreplay to use Libnet to send packets
- –enable-force-inject – force tcpreplay to use Libpcap’s pcap_inject() API to send packets
- –enable-force-sendpacket – force tcpreplay to use Libpcap’s pcap_sendpacket() APIto send packets
If you’re having compatibility issues with a system-installed GNU Autogen,you may want to consider these options:
- –disable-local-libopts – Don’t use the libopts tearoff supplied with tcpreplay(default is enabled)
- –disable-libopts-install – don’t install the libopts library files

Special Instructions for Windows
Consider Windows support for Tcpreplay is experimental - beta quality if you will.We strongly recommend you read the page about how to get support for Tcpreplay.
Tcpreplay Edit
With that said, you’ll need Cygwin to compile/run tcpreplay. You’ll also need to installWinpcap - the port of libpcap for Windows. For whatever reason, it seems importantthat you install the Winpcap files in the Cygwin root directory (/Wpdpack).
Be sure to install both the driver and DLL files AND developer pack.Then when you run./configure, you’ll need to specify the location for Winpcap using the --with-libpcapflag, but use all lowercase: ./configure --with-libpcap=/wpdpack.
After that, for the most part things should just work. There are some caveats; a fewfeatures and make test don’t work, but for the most part they seem to be pretty minor.
For more detailed instructions, see the Win32Readme.txt.
Note: We’ve been informed that the guile Cygwin package is broken.This horribly breaks parts of GNU Autogen - specifically the parts whichallow you to build Tcpreplay via GitHub. Hence, I strongly recommend grabbinga tarball release.
How To Install Tcpreplay On Windows10
Need Help?
How To Install Tcpreplay On Windows 10
Having problems? Try asking for help on thetcpreplay-users mailing list or check out the Support section.